A virus is the simplest form of what is commonly thought of as “life”. Many viruses consist of nothing more than a single strand of DNA wrapped in a protein casing, although they sometimes have additional structural features that perform rudimentary functions.
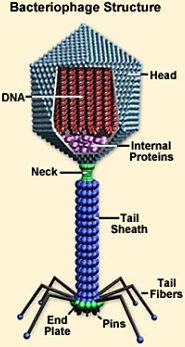 The bacteriophage is one of the most well-known types of viruses. In addition to its capsule of DNA, it features a columnar tail with a base plate. Attached to the plate are fibers that look like the legs of a landing craft, which bring the base plate into full contact with the target bacterium at specific receptors on the victim’s cell wall using special pins. After the virus attaches itself, the tail contracts, injecting viral DNA into the host cell. The invader’s DNA then hijacks the host cell’s ribosomes, forcing them to build new viruses rather than perform their normal functions. After a sufficient number of new viruses have been assembled, the cell wall is destroyed, and a new generation of viruses is released into the environment to repeat the cycle with other bacteria.
The bacteriophage is one of the most well-known types of viruses. In addition to its capsule of DNA, it features a columnar tail with a base plate. Attached to the plate are fibers that look like the legs of a landing craft, which bring the base plate into full contact with the target bacterium at specific receptors on the victim’s cell wall using special pins. After the virus attaches itself, the tail contracts, injecting viral DNA into the host cell. The invader’s DNA then hijacks the host cell’s ribosomes, forcing them to build new viruses rather than perform their normal functions. After a sufficient number of new viruses have been assembled, the cell wall is destroyed, and a new generation of viruses is released into the environment to repeat the cycle with other bacteria.
Viruses that target multicellular organisms function in a similar manner. However, they have of necessity evolved genetic strategies of greater complexity in order to exploit their more complex hosts. To reach the tissues they have evolved to target, they must make their way past the immune defenses that their hosts have developed to thwart them. A weakened organism whose immune system has been compromised by age, injury, stress, famine, or previous bouts of infection is more vulnerable to an attack by invading viruses.
A strategy that includes the weakening of a host’s immune system thus becomes a useful part of a well-tailored virus’ wardrobe. Viruses that cause autoimmune diseases — HIV is the most well-known example — attack the host’s immune system directly.
 Analogous behavior is exhibited by the computer viruses used to target cybernetic systems. Labeling these snippets of code “viruses” is apt: their modus operandi is directly analogous to that used by biological viruses that attack living organisms.
Analogous behavior is exhibited by the computer viruses used to target cybernetic systems. Labeling these snippets of code “viruses” is apt: their modus operandi is directly analogous to that used by biological viruses that attack living organisms.
As soon as it has been inadvertently downloaded, the first action attempted by a well-tailored piece of “Trojan horse” malware may be to disable the target’s virus-protection software. It overwrites the antivirus system’s database of malicious code signatures, removing any reference to itself as a malicious entity. After that it masquerades as virus protection and announces that the user’s computer has been infected. Typically it offers additional software for sale, which it says is necessary to remedy the problem.
This and other malicious strategies may do serious damage to the host system, sometimes disabling it completely and necessitating a rebuild of the computer.
The virus analogy may be extended to other complex information systems. Any system that is sufficiently complex is also vulnerable to malicious intrusion. A packet of information from outside the system may mimic the characteristics of some part of the system, providing appealing “hooks” to induce its incorporation. Then, once it is fully integrated into the substrate of its host, it begins to replicate itself, using internally encoded instructions to disable further resistance on the part of the surrounding system.
After that the invader spreads, gradually replacing components of its host with its own simulacra. Its replacements may not be fully functional, but they only have to serve until the invader’s purpose has been accomplished — which is usually to suck all useful sustenance/information from the system before moving on to other uninfected hosts.
By now regular Gates of Vienna readers will have noticed the resemblance between invading viruses and a certain Religion of Peace…
Continue reading →
 A 14-year-old “Austrian” boy has been convicted of plotting to blow up Vienna’s main railway station. According to prosecutors, he was radicalized by Al Qaeda and other kinetic activists online, and downloaded bomb-making plans onto his PlayStation. He was sentenced to two years of confinement, with fourteen months suspended. With time served, he will serve three months in juvenile detention.
A 14-year-old “Austrian” boy has been convicted of plotting to blow up Vienna’s main railway station. According to prosecutors, he was radicalized by Al Qaeda and other kinetic activists online, and downloaded bomb-making plans onto his PlayStation. He was sentenced to two years of confinement, with fourteen months suspended. With time served, he will serve three months in juvenile detention.

 In his practice, Mayer has studied what an example such youngsters are for criminals. Speaking with the Wiener Zeitung, the attorney gives his account of domestic integration policy. He considers it a failure.
In his practice, Mayer has studied what an example such youngsters are for criminals. Speaking with the Wiener Zeitung, the attorney gives his account of domestic integration policy. He considers it a failure.



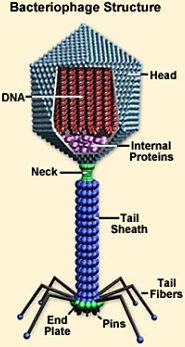 The bacteriophage is one of the most well-known types of viruses. In addition to its capsule of DNA, it features a columnar tail with a base plate. Attached to the plate are fibers that look like the legs of a landing craft, which bring the base plate into full contact with the target bacterium at specific receptors on the victim’s cell wall using special pins. After the virus attaches itself, the tail contracts, injecting viral DNA into the host cell. The invader’s DNA then hijacks the host cell’s ribosomes, forcing them to build new viruses rather than perform their normal functions. After a sufficient number of new viruses have been assembled, the cell wall is destroyed, and a new generation of viruses is released into the environment to repeat the cycle with other bacteria.
The bacteriophage is one of the most well-known types of viruses. In addition to its capsule of DNA, it features a columnar tail with a base plate. Attached to the plate are fibers that look like the legs of a landing craft, which bring the base plate into full contact with the target bacterium at specific receptors on the victim’s cell wall using special pins. After the virus attaches itself, the tail contracts, injecting viral DNA into the host cell. The invader’s DNA then hijacks the host cell’s ribosomes, forcing them to build new viruses rather than perform their normal functions. After a sufficient number of new viruses have been assembled, the cell wall is destroyed, and a new generation of viruses is released into the environment to repeat the cycle with other bacteria. Analogous behavior is exhibited by the computer viruses used to target cybernetic systems. Labeling these snippets of code “viruses” is apt: their modus operandi is directly analogous to that used by biological viruses that attack living organisms.
Analogous behavior is exhibited by the computer viruses used to target cybernetic systems. Labeling these snippets of code “viruses” is apt: their modus operandi is directly analogous to that used by biological viruses that attack living organisms.