A virus is the simplest form of what is commonly thought of as “life”. Many viruses consist of nothing more than a single strand of DNA wrapped in a protein casing, although they sometimes have additional structural features that perform rudimentary functions.
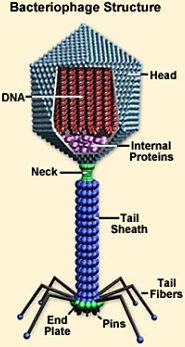 The bacteriophage is one of the most well-known types of viruses. In addition to its capsule of DNA, it features a columnar tail with a base plate. Attached to the plate are fibers that look like the legs of a landing craft, which bring the base plate into full contact with the target bacterium at specific receptors on the victim’s cell wall using special pins. After the virus attaches itself, the tail contracts, injecting viral DNA into the host cell. The invader’s DNA then hijacks the host cell’s ribosomes, forcing them to build new viruses rather than perform their normal functions. After a sufficient number of new viruses have been assembled, the cell wall is destroyed, and a new generation of viruses is released into the environment to repeat the cycle with other bacteria.
The bacteriophage is one of the most well-known types of viruses. In addition to its capsule of DNA, it features a columnar tail with a base plate. Attached to the plate are fibers that look like the legs of a landing craft, which bring the base plate into full contact with the target bacterium at specific receptors on the victim’s cell wall using special pins. After the virus attaches itself, the tail contracts, injecting viral DNA into the host cell. The invader’s DNA then hijacks the host cell’s ribosomes, forcing them to build new viruses rather than perform their normal functions. After a sufficient number of new viruses have been assembled, the cell wall is destroyed, and a new generation of viruses is released into the environment to repeat the cycle with other bacteria.
Viruses that target multicellular organisms function in a similar manner. However, they have of necessity evolved genetic strategies of greater complexity in order to exploit their more complex hosts. To reach the tissues they have evolved to target, they must make their way past the immune defenses that their hosts have developed to thwart them. A weakened organism whose immune system has been compromised by age, injury, stress, famine, or previous bouts of infection is more vulnerable to an attack by invading viruses.
A strategy that includes the weakening of a host’s immune system thus becomes a useful part of a well-tailored virus’ wardrobe. Viruses that cause autoimmune diseases — HIV is the most well-known example — attack the host’s immune system directly.
 Analogous behavior is exhibited by the computer viruses used to target cybernetic systems. Labeling these snippets of code “viruses” is apt: their modus operandi is directly analogous to that used by biological viruses that attack living organisms.
Analogous behavior is exhibited by the computer viruses used to target cybernetic systems. Labeling these snippets of code “viruses” is apt: their modus operandi is directly analogous to that used by biological viruses that attack living organisms.
As soon as it has been inadvertently downloaded, the first action attempted by a well-tailored piece of “Trojan horse” malware may be to disable the target’s virus-protection software. It overwrites the antivirus system’s database of malicious code signatures, removing any reference to itself as a malicious entity. After that it masquerades as virus protection and announces that the user’s computer has been infected. Typically it offers additional software for sale, which it says is necessary to remedy the problem.
This and other malicious strategies may do serious damage to the host system, sometimes disabling it completely and necessitating a rebuild of the computer.
The virus analogy may be extended to other complex information systems. Any system that is sufficiently complex is also vulnerable to malicious intrusion. A packet of information from outside the system may mimic the characteristics of some part of the system, providing appealing “hooks” to induce its incorporation. Then, once it is fully integrated into the substrate of its host, it begins to replicate itself, using internally encoded instructions to disable further resistance on the part of the surrounding system.
After that the invader spreads, gradually replacing components of its host with its own simulacra. Its replacements may not be fully functional, but they only have to serve until the invader’s purpose has been accomplished — which is usually to suck all useful sustenance/information from the system before moving on to other uninfected hosts.
By now regular Gates of Vienna readers will have noticed the resemblance between invading viruses and a certain Religion of Peace…
Human cultures are complex information systems. Like all such systems, they are subject to infection by analogues of viruses. When a malicious component of one culture invades another, it may behave exactly like a biological virus in a cell, or malware in a computer.
To continue the analogy of the bacteriophage, the organelles of the host are analogous to our cultural institutions. The ribosomes might be the industrial plant, while the endoplasmic reticulum would correspond to networks for transportation and communication, the mitochondria to power plants, and so on. And some combination of institutions — churches, universities, and media, perhaps — functions as the cultural nucleus for our society. The basic characteristics of our culture are recorded there, and in addition a mechanism for replicating them from generation to generation.
It is into this informational matrix that the virus of Islam has injected itself. And Islam is not just an ordinary virus — it has all the characteristics of an autoimmune disease. The first thing it does when it invades a society is to find the institutions that protect the culture, discover how they work, and disable them. When the host society’s institutions have been significantly weakened, they can be converted gradually to Islamic institutions, after which the spread of Islam throughout the culture is expedited and accelerated.

Islamized institutions function less effectively than the host’s versions, but that is no impediment to the spread of Islam. The Islamic virus is a classic parasite: it extracts as much useful sustenance from its host as it can, leaving just enough of the original structure in place to assure that system continues to function for its benefit. The host society may eventually be severely damaged or destroyed, but that is of no concern to Islam — by then it is ready to use the platform of its debilitated host to inject itself into yet another victim.
It is commonly stated that Islam is a political ideology disguised as a religion, but it is even more than that: Islam is political malware. It is superbly adapted to invade alien political systems and convert them into replication machines for more Islam. The infection of Europe has now advanced sufficiently to allow the launch of thousands upon thousands of jihad vectors into other parts of the world.
When Islam realizes its final goal and achieves world domination, it will be like a parasite that has killed off its host and has no others to jump to. At that point it will self-destruct, but the occasion will hold no consolation for non-Muslims, since there won’t be any left.
The autoimmune characteristics of the Islamic disease were enhanced by the weakened cultural immunity of the West, which had been significantly degraded over several decades before Islam arrived. The forces of deliberate cultural destruction — neo-Marxism, cultural Marxism, political correctness, call them what you will — had already degraded and hollowed out our traditional institutions when the first imams began spouting their Friday sermons from the pulpits of brand new Saudi-sponsored mosques.
The “root causes” of the Great Jihad in the West are thus to be found not within Islamic societies, but within the West itself. Our cultural immune system was severely weakened well before 1980. Islam just saw the opportunity, and seized it.
The Islamic virus functions as a kafirophage — it invades and devours what it calls “kafir” societies, which it defines as any that are not Islamic. Western Civilization serves as the kafir-of-the-moment.
Can a host that is already severely compromised by such a massive infection repair its immune defenses sufficiently in time to fend off the invader?
The chances don’t look good. The final outcome won’t be known in my lifetime, but if you’re under forty-five, you may live to see it — if the mujahideen let you live, that is.
Or like the more primitive prion that invades the brain of cannibals and causes Kuru, ~The Laughing Death.
Although there’s nothing funny about Islam.
Baron,
This sounds like a cry of despair and I totally sympathise.
Regardless of the efforts of GoV and others, the jihadists seem to be winning on all fronts.
I find it hard to be positive these days….
I always ask myself: what would your “intellectual ancestors”, viz. the Ancient Greeks, do in this situation? – The answer is quite clear in my rather naive enchantment with them: THEY WOULD FIGHT TO THE LAST MINUTE AND LAST DROP OF THEIR BLOOD. We must be like them: I have never thought that my generation will see the rise of fascism … just happening. Sharia-fascism is even uglier than the German national version of it: instead of one nation there is that huge Ummah, instead of “cold supremacist cruelty” there is ardent barbarism and unutterable insanity against the whole West.
I may see the bitter future if I live long enough. Old man in Texas with his guns and fighting … like my beloved Greeks. Sad but quite possible.
The MSM reaction to the incident in Garland, Texas was awful.
The “Chinks” The “Japs” and possibly Russia will be the last bastions.
None of our bastions have taken any action yet. If they ever do – Islam and its Mudlims are screwed. Maybe a coup d’état or two led by the police and armed forces backed up by millions of organized and very very angry civilians will get the job done.
The Chinese may be Islam’s Waterloo. But the Chinese have no history of leaving the “Central Kingdom”. But they do have a history of destroying all invaders.
The Chinese are showing significant action against the Wieger Muslim Chinese population.
The rest of the world is toast if it does not drop the PC mindset.
I would point out that Israel is in a shooting war with Islam and winning, apart from the fact that the rest of the world howls with rage and threatens mayhem every time Israel is on the verge of eliminating the canker.
The West (and the Pope) prefers Palestinian propaganda and lies to the idea that Joos also have ‘rights’.
If the West goes under and the world reverts to pagan barbarism, nobody benefits except maybe the elites who can make the transition to a new feudal Aristocracy. And then they too would be at the mercy of Islamic violence.
Destroy Judeo-Christian values and you destroy civilization itself. Only whitey pays the bills.
The elites think that, at the right time they can pull the plug, but somehow I think they have miscalculated.
It would appear that at least some of the Traitor Class are embracing Islam as the ‘new kid’ on the block which they see as their own longevity as an elite within, that is if Islam sees fit to acknowledge their conversion while allowing them to personally retain their ill gotten gains with a status of some kind.
But the many who have got us into this mess, I would venture, have done so out of sheer greed and love of power over those they have been taught to hate – their own kind. They would make up the dominant numbers within the Traitor Class and it is those who must be dealt with before we can tackle Islam and the elite within the Traitor Class.
Make no mistake, while the Traitor Class believes it is winning in the ideological stakes against a demoralized and decaying West they have assisted in bringing about, they are still wary of the grass roots uprising which can occur at some time in the future – they just do not know at what time or how determined that uprising may be.
Does anyone truly believe that Jade Helm was just another military exercise?
Well, nobody with any military background, because if you know anything about how actual military exercises are run you realize instantly that Jade Helm was a propaganda exercise.
Israel communicates clearly. ISIS communicates clearly.
A great analogy Baron! What a pity that the majority are still stuck to their sport and that lying god in the corner. Still, I can also see where many of us are now awake to the threat that is Islam, and where the Traitor Class have had over a century of treasonous activity, we who are aware, are just getting started.
So, it is still early days yet to forecast whatever the outcome will be.
Perfect analogy, although we have fought it before, many times, and have done pretty well. Thus it is not, historically, a perfectly lethal virus, like rabies. I wonder, however, if it has mutated, since Qutb, into a more deadly strain.
Indices of lethality:
Acquires money, land, and educated people that is uses as capital ( think tools)
Acquires science
Acquires WMD
Here’s something I wrote 9 years ago at Jihad Watch…
jsla says
September 25, 2006 at 4:34 pm
“Just the contents of Gourmet, or Leisure & Travel, or Conde Nast Traveller, with all those “Lorenza de’ Medici” condiments for sale?” — from poster above
Sadly and foolishly, many in the West have come to view these things and many more as ‘givens’. To that list we can also add the Bill of Rights and computer chips. There are no guarantees that those things are forever, and it’s the height of folly to believe they might be. These things are powerful, but also fragile. If such things are taken for ‘granted’ such things become extremely brittle and precarious. Over the long span of time, the only things which last are the things which are valued beyond all others, and tended with great care.
As for “…Abou Jahjah’s notorious statement that “assimilation is cultural rape”; this sadly corresponds directly to the poisonous post modern anti-colonialist Western notion that “assimilation is cultural rape” as long as it’s the West which is doing the imposing, but not the other way around.
How ludicrous, for example, is the idea that our newscasts and local governments often list “Kwanzaa” along with Hannakuh or Christmas in an attempt to be ‘culturally inclusive’ and ‘sensitive’?
Kwanzaa is nothing more than a cynical hoax — It’s an invention by a radical black seperatist bent on harming Western Culture and increasing the divisions between the races — in short — a Black Racist. Now this swill is widely and unquestioningly embraced. The ‘inventor’ of this fake, ludicrous, and degrading ‘pan African’ ‘celebration’ was a black panther, and an anti-American communist insurrectionist. Steeped in all kinds of stupid, preposterous and insulting mumbo jumbo which only serves to perpetuate unpleasant stereotypes of Blacks in America, we all meekly play along rather than objecting to the harm it causes. God forbid that the things I say would ever be brought up in ‘mixed’ society. (that would be any group of thinking adults mixing with child-like post modern leftist deconstructionists for example — race has nothing to do with what I’m saying…)
But it’s a classic example of the way even racist spurious and despicable hoaxes are given credence if they even have the appearance of emanating from non-White non-Western culture and are being imposed in the West…
I’d suggest that a white racist could hardly have come up with a better ‘holiday’ to marginalize and stigmatize blacks in America than Kwanzaa. Take a look at the bilious swill at the “Official Kwanzaa Web Site” by the concoctor of said ‘celebration’.
http://www.officialkwanzaawebsite.org/index.shtml
Somehow telling the truth these days, or contemplating the idea that one culture may be superior to another is so anathema that such discussions are unutterable in public, unless the discussion is about how non-White non-Western non-Christian culture is always better, or that the only reasons non-White non-Western non-Christian cultures suffer is because of something the White Western Christian culture did, is doing, or will do.
THIS is the disease we suffer from in the West. THIS is the hole we’ve bashed in the protective walls around our society. Having somehow been persuaded by the ‘elite’ in the West that such walls are a bad thing, or that the such walls are no longer necessary we have allowed ourselves to become mortally compromised. This is the same hole through which the batallions of Islam are pouring in their millions into our dominions. This is our modern day idolatry.
In an irony for the ages, the breach we’ve created ourselves is the same breach that the Muslims intuit our weaknessess and our susceptibility and our apparent unwillingness to fight for our heritage. It’s the one thing I agree with the Muslims about:
We are a decadent society ripe for takeover. We’ve volunteered to lay ourselves at the alter of our false beliefs in this manner. It doesn’t matter if such things were done with the best of intentions. And whether we deserve to be annihilated is an altogether different question. I think I’d disagree with most Muslims on whose beliefs should be annihilated, but I see their point.
I’m coming to believe that Islam is a symptom of an immuno-compromised culture. To the extent that Islam is flourishing is the extent to which that culture has already lost the battle to protect itself against opportunistic infection. And the infection of Islam is most ominous for it plays on all the other social ills which have always haunted society — it feeds on chaos, dissention, hopelessness, backwardness, and lack of confidence.
Islam is happy to fill those breaches in us. It is one of the only thing Islam excels at.
“The chances don’t look good.”
The wonderful Canadian writer Dave Soloway agrees…
http://pjmedia.com/blog/later-than-we-think/?singlepage=true
I was so surprised when I saw this article because since I heard the news that the Irish voted for same-sex marriage in a landslide, I began to think about the condition of the West as that of a compromised organism, such as a plant that did not receive proper care and succumbed to some type of disease or as an immunocompromised human being ravaged by opportunistic infections and diseases that would not be a threat to a normally intact human. It seems like a law of nature: there are always opportunists around ready to pounce on and consume an organism in a weakened state. One can observe this throughout nature. Because the West now has shown itself to be out-rightly lacking in confidence in itself and its lack of will to protect its heritage, its reason to be, and even acting unnaturally, it is natural for an opportunistic scavenger to move in and remove the unfit-to-live entity called the West. Maybe that is the function of Islam today for the West. If it weren’t Islam, then it might have been something else. It just so happens that it looks like Islam is the agent. Maybe we are at the point of being unfit, due to some cause or a complex of causes, for continued existence in our present form and must suffer the consequent fate of being in such an unfit condition. Like the AIDS patient being consumed by an opportunistic infection and teetering on the point of death, are we near the point of death also, if only to be saved by outside intervention? Is there a treatment? Is there still time to save the organism? Or is it too late? Or are we living in a time as our pre-modern forebears who knew nothing of microbes and therefore death from a serious infection was an inevitable outcome for them, and maybe for our civilization in our case? And should or can one look on the situation purely from a dispassionate, clinical, scientific point of view? Maybe if one is outside of the entity being consumed, one can view this dispassionately. But if one is a member of the entity being consumed, it does not seem rational or natural to be dispassionate.
I actually think getting the liberals on our side is the only hope (due to sheer numbers). I’m starting to emphasise, in every laborious discussion with my mid-left-liberal friends, that our liberal culture must not support a sexist, homophobic ideology and that opposing this ideology is not racist. I think it’s starting to sink in with some people…
“Somehow telling the truth these days, or contemplating the idea that one culture may be superior to another is so anathema that such discussions are unutterable in public, unless the discussion is about how non-White non-Western non-Christian culture is always better, or that the only reasons non-White non-Western non-Christian cultures suffer is because of something the White Western Christian culture did, is doing, or will do.
THIS is the disease we suffer from in the West…”
Quite true and worse it is the mothers milk of what is taught in our public schools and even the Ivy Leagues. They are intellectually pickled in a brew of subjectivism for several decades before being unleashed upon the world. This ‘education’ disarms both the elites and the lower classes. As a result they look at a Muzzie as “the other” a poor benighted 3rd worlder who deserves our unequivocal support no matter what. This along with subjectivism turns them into millions of mindless Eloi’s when confronted by psychopaths on a rampage like those at Garland TX. The intellectual, news and political elites in this country who are also the primary consumers of such suicidal idiocy could only respond with fear and condemnation for the presenter of the convention, not the dead fanatics. Worse, almost all products of our finest educational establishments.
C.S. Lewis saw it coming almost 60 years ago when he penned the “Abolition of Man” about the introduction of relativism in high school and how it produced “men without chests”.
It seems like what has happened is that, as the degree of interconnection has increased due to technology (extremely high speed transportation and communication), humans have been overwhelmed and have attempted to cope with this psychologically by declaring that “all views are equally valid and lead to the same results” (extreme subjectivism).
As the difficulty of reconciling cultural incompatibilities has increased due to sheer diversity, the response of the “intellectual” leaders, and thus the average person, has been to deny that these incompatibilities exist rather than deal with them. It’s the same as being so overwhelmed with responsibility that you just give up.
This is sort of like an immune system being overwhemed by so many different potential pathogens that it can’t produce enough of all of the different antibodies needed to fight off all of them while also being unable to determine what potential pathogen is actually a real threat. This is the sort of situation that western civilization is in, except that most of the immune system has been attacking its own organism instead of examining potential pathogens.
The autoimmune disease started with the cultural attack from Marxism-Communism (critical theory). That was the HIV, and Islam is just the pneumonia that is taking advantage of the weakened host now.
Another useful analogy to Islam that is found in nature is the Parasitoid Wasp. These wasps inject their eggs into healthy insect and larvae hosts. The baby wasps feed off the oblivious host, and by the time the wasps emerge to fly away, the host is dead, consumed from within. You can see various youtube videos of this process if you wish. I created a meme highlighting this Parasitoid Wasp/Islam analogy.
https://scontent-atl1-1.xx.fbcdn.net/hphotos-xfp1/v/t1.0-9/11009144_955608064458634_7241568946459395393_n.jpg?oh=bad09ec4da88f9df562e7a6748e785c6&oe=55FDB80E
Another analogy closely related to that of biology is that of the meme. Ideas, like pathogens may spread in epidemic fashion. An idea or a linked constellation of ideas are subject to natural selection like genes. Religions, philosophies, ideologies are examples of such memes; those adapted to the conditions or circumstances of the time persist and spread. Quotes are from Howard Bloom, The Lucifer Principle.
“Memes are ideas, the snatches of nothingness that leap from mind to mind. … A melody wells up in the reveries of a solitary songwriter. It seizes the brain of a singer. Then it infects the consciousness of millions. … But the memes that count the most are the ones that assemble vast arrays of resources in startling new forms. They are the memes that construct social superorganisms.”
Islam is one such meme; a particularly formidable one that once besieged much of the world and has now experienced a second birth:
“The modern growth of Islam is the coalescence of a superorganism drawn together by the magnetic attraction of a meme. But this meme has an advantage: The social body it is trying to pull together has existed as a unified social beast in the past. The old reflexes of solidarity are still there, waiting to be aroused. The meme of the new Islam is not laboring to generate a small and fragile embryo. It is simply attempting to awaken a sleeping giant.”
Ridicule, cartoons, satire, severe criticism, argumentation, denigration, sarcasm, scorn, contempt, parody… all this stuff that we brought against tobacco and drunk driving worked, didn’t it? Maybe it would help fight Islam and turn apostates a bit? Why not? We all affect one another. Do we make more jihadists or fewer by doing this? There might be an actual answer to this question. IMHO we should let loose on them–full bore whacking–just as we would for any other bad idea.
Oh yes, and we need to emphasize how plain puerile and bestial Islam is too, none of this all cultures are equal garbage.
Some times ago Dymphna has written a brilliant comment about one of the reasons why many western youths turn to Islam. This one of the reasons is the militant and mindless feminism.
“The “root causes” of the Great Jihad in the West are thus to be found not within Islamic societies, but within the West itself. Our cultural immune system was severely weakened well before 1980. Islam just saw the opportunity, and seized it.”
That’s the heart of it right there. And that’s why I think that the virus analogy misses just a bit. The Islam virus didn’t further weaken our already weak immune system or overwhelm it through mutations. It’s not a Trojan Horse that has cleverly deceived us. The West appears to have no immune system at all. You don’t need a virus to conquer such a host. You just walk through the front door.
Islam today is what it has always been. We’ve had hundreds of years to observe its behavior in the clear sunlight. And it’s always the same wherever it goes. It’s no sneaky virus.
Islam is wreaking havoc in the West today because we opened our doors and welcomed it in. After observing its track record for over a 1000 years we invited it into our home. Islam deserves no credit for such a victory. If it wins it will only be by default because the opponent refused to show up for the match.
The Islam virus didn’t further weaken our already weak immune system or overwhelm it through mutations. It’s not a Trojan Horse that has cleverly deceived us. The West appears to have no immune system at all. You don’t need a virus to conquer such a host. You just walk through the front door.
Islam today is what it has always been. We’ve had hundreds of years to observe its behavior in the clear sunlight. And it’s always the same wherever it goes. It’s no sneaky virus.
It’s ‘sneaky’ in the sense that it lies about its intents and purposes. But even when the MB tells the truth about its plans for the destruction of our miserable house, it is roundly ignored by the intelligentsia, since that doesn’t fit its narrative about the “brown victims” of America. It would be funny were it not so lethal.
I agree that we opened our doors, but this is the foundation of the process of becoming an American; we open our doors and immigrants enter to start a new life. It’s been going on now for several centuries. We used to safely assume those coming in wanted to prosper using the same process of assimilation that successful immigrants in the past have used.
However, that’s not true for everyone. The Sicilian Mob used our welcome mat in some ugly ways. And now many South American terrorists and drug “lords” are doing the same, though the latter is far more open about it. As are the Russians, Pakistanis, Albanians, etc.
From the Muslim branch of Mayhem, one such person who was welcomed, Sayyid Qutb, later returned home to be jailed and hung by Nasser after founding the Muslim Brotherhood.
http://en.wikipedia.org/wiki/Sayyid_Qutb
Sadly, some of what Qutb says in his observations of America is true – but he carried it to the point of caricature, finding even church dances to be evil (this was in 1949), unchaperoned mixing of the sexes (he never married, by the way).
His associate, the grandfather of Tariq Ramadan (fondly know to Gates of Vienna readers as Taqiyya Ramadan), wasn’t hung but was exiled to Switzerland. The Swiss Defence League has some information on him:
https://swissdefenceleague.wordpress.com/2012/12/04/the-world-view-of-hasan-al-banna-and-the-muslim-brotherhood/
———————————————–
Occidentalism: A Short History of Anti-Westernism
The blurb from the page:
In this book, Ian Buruma and Avishai Margalit show that the idea of ‘the West’ in the minds of its self-proclaimed enemies is still largely unexamined and woefully misunderstood. Occidentalism is their groundbreaking investigation of the demonizing fantasies and stereotypes about the Western world that fuel such murderous hatred in others. ‘Radical Islam’ is generally perceived as a purely Islamic phenomenon, but Buruma and Margalit show that groups like al-Qaeda share key traits with revolutionary movements going back to the early nineteenth century. The same prejudices appear again and again: the soulless Western city-dweller, the sterile Western mind, the machine society, controlled from the centre – often by Jews – pulling the hidden levers of power, like some demonic Wizard of Oz. The anti-Western virus has spread to the Islamic world for a number of reasons, but it is not an exclusively Islamic issue. A work of extraordinary range and erudition, Occidentalism will permanently enlarge our understanding of the world in which we live.
“It’s ‘sneaky’ in the sense that it lies about its intents and purposes.”
When it comes to politics on the world stage I’ve always assumed every country takes it as a beginning premise that it’s going to be lied to on a regular basis. During the cold war we surely didn’t believe a single thing the Soviet Union said to us. “Trust but verify” as Reagan said. So when the Muslim Brotherhood lies to us I think of it as business as usual for power politics. Rather than thinking of them being sneaky it seems more like we’re being naive and foolish by listening to a single thing they say.
“…we open our doors and immigrants enter to start a new life.”
Yes, I agree this has been a long held foundational belief in America But as time passes a nation interested in its own welfare will always need to reassess its behavior. Right now there are over 300 million people in America. And we’re bankrupt. Do we really need more unskilled immigration at this point?
“We used to safely assume those coming in wanted to prosper using the same process of assimilation that successful immigrants in the past have used. ”
Yes, agreed. And that worked in the past, before we had a huge welfare state. But by now, as you noted with the South Americans, Russians etc., it’s becoming clear that immigrants, especially third world immigrants, aren’t coming here because they love Jeffersonian democracy or want to assimilate and become Americans. Yet we still import them at a rate of approximately 1 million a year. What possible benefit is this to us?
And when it comes to Muslim immigration all we have to do is look to Europe to see where we are going to be in a very short time. And the depressing part is it seems like most Americans just don’t care.
Yearning to ‘breathe free’ has become yearning to ‘live for free”
“The forces of deliberate cultural destruction — neo-Marxism, cultural Marxism, political correctness, call them what you will — had already degraded and hollowed out our traditional institutions…”
This description (particularly the use of the word “deliberately”) doesn’t adequately explain why, for example, the conservative academics of the Eric Voegelin Society (revolving around their mentor, Eric Voegelin, himself profoundly opposed to Marxism, diagnosing it as a “pneumopathology”) tend to parrot and regurgitate the memes of PC MC about the problem of Islam.
What you are describing implies that the early efforts of what is now called the Frankfurt School were quite effective. Their “deconstruction” was deliberate and intentional, as their writings show. As their work percolated through academia, many others — including some “conservatives” — absorbed the new Weltanschauung, presumably without realizing it.
Obviously, I can’t assert the preceding description as definitively true without tracking back through detailed historical material. But it at least has the merit of being reasonably plausible.
Dawkins on religous pestilentia .
Most interesting from ca 50% to 100%.
https://youtu.be/9FiHRVb_uE0
https://youtu.be/9FiHRVb_uE0
This is the correct link!!!!!!!!
Ideologies like Islam, which promotes hatred and the destruction of all that is not Islam, need to have vaccines in place through education. And by education, I mean that the ideology must be exposed for all it’s worth, deadly warts and all.
Sadly, what the west has done is value tolerance for all ideologies and cultures in a misguided attempt to demonstrate how much “better” the west is than Islam, Communism or any other ideology which seeks world domination by any means necessary. Accepting bogus refugees since the late 80s has shown Muslim leaders that the west is weak and will allow jihad to flow from Muslim countries through the migration of Muslims to the west.
If western scholars and politicians were honest about Islam, it would be banned as a subversive political organization whose followers are determined to overthrow any government and culture that is not Muslim.
The world needs to see Islam as the exception to the rule that religions are beneficial to the world and that they are spiritual in nature. Islam is nothing if not political, greedy and dangerous to have around.
We need a world-wide vaccine to prevent the Islamization of the planet. Sites like this should be put front and center in that vaccination program.